Mastering Flowtriq for Sub-Second Network Defense
2d4oiag|Saturday, February 28, 2026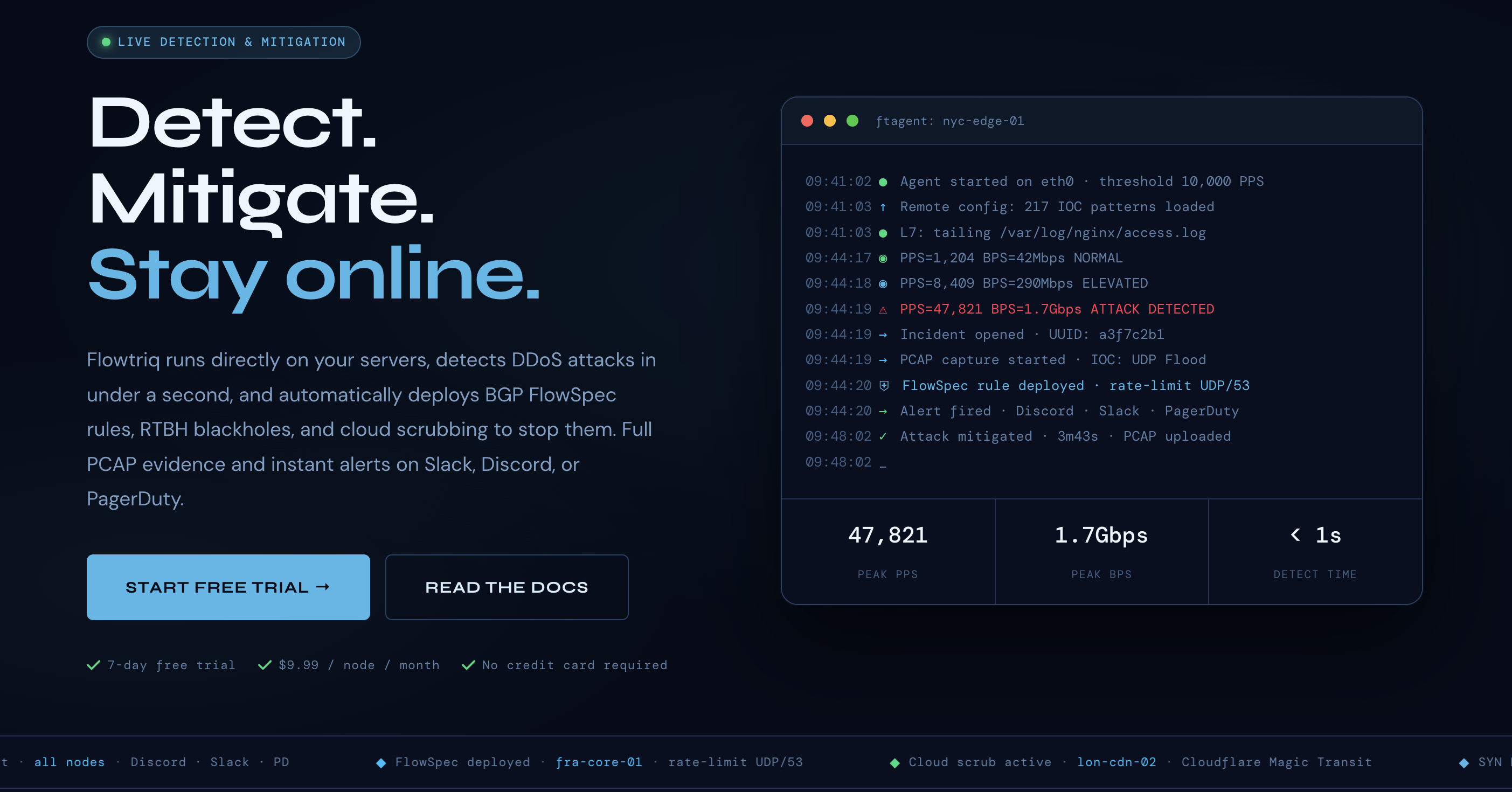
Network-layer attacks must be stopped before an engineer can read an alert.
Sub-second network defense: Flowtriq at the packet edge
Flowtriq is a lightweight, agent-centric DDoS detection and auto-mitigation platform designed to detect and neutralize volumetric and application floods in under one second. The core stack centers on ftagent — a Python-based agent that reads packets directly from the NIC, streams telemetry to a cloud dashboard, and enforces automated escalation policies (BGP FlowSpec, RTBH, cloud scrubbing). The design philosophy favors fast, local decisions (per-second PPS checks and anomaly detection) with cloud orchestration for centralized policy, audit logs, and attack forensics. The vendor pairs this with a large IOC database (≈642k indicators), published DDoS research, and a library of free operations tools — positioning Flowtriq as a practical, operator-first solution for hosting providers, ISPs, game hosts, and SaaS operators.
Architecture & Design Principles
Flowtriq follows a hybrid edge+cloud model. The ftagent runs on Linux (root-level packet capture via AF_PACKET or similar) and performs local baseline learning, per-second PPS analytics, and IOC matching. When an anomaly is detected, the agent triggers a cloud-managed orchestration pipeline that can: (1) push BGP FlowSpec rules to upstream routers, (2) request RTBH blackholing, or (3) engage cloud scrubbing (Cloudflare Magic Transit, OVH VAC, Hetzner) according to user-defined escalation policies. Key technical decisions: keep detection local to minimize network RTTs, use cloud for centralized correlation, and persist immutable audit logs and PCAPs for post-incident analysis. Scalability is achieved by decentralized packet processing (each node monitors its NIC) and centralized rule coordination for multi-node mitigation campaigns.
Feature Breakdown
Core Capabilities
- Sub-second detection & classification: Per-second PPS sampling with classifiers for SYN flood, UDP/DNS/memcached amplification, ICMP, HTTP and Layer-7 anomalies. Use case: an unexpected SYN spike triggers immediate FlowSpec rules to drop offending tuples before session tables overflow.
- Auto-mitigation playbooks: Chainable runbooks map detection to actions — FlowSpec → RTBH → cloud scrub — so escalation can be automatic or stepped. Use case: gaming server sees UDP flood; Flowtriq first applies granular FlowSpec filters, then escalates to scrubbing if rates persist.
- Forensics & IOC correlation: Automatic PCAP capture on every attack with IOC matching against a 642k+ indicator corpus and attack profiles. Use case: post-incident attribution of a Mirai-variant flood using matched botnet signatures and preserved PCAPs.
Integration Ecosystem
Flowtriq exposes multi-channel alerting (Slack, Discord, PagerDuty, OpsGenie, SMS, email, webhooks) and integrates with major scrubbing providers and upstream routers for FlowSpec/RTBH. The platform provides webhooks and a cloud dashboard for multi-node management, and a suite of free tools (FlowSpec builder, PCAP analyzer). API coverage is geared toward operations automation — teams can slot Flowtriq into existing incident pipelines and status pages.
Security & Compliance
Data-handling choices prioritize forensic fidelity: immutable audit logs and automated PCAP retention (365-day retention available on enterprise plans). The platform runs security research (e.g., Mirai kill switch CVE-2024-45163) and offers custom IOC libraries for enterprise customers. The vendor does not list public compliance certifications in the provided material, so organizations should validate SOC2/GDPR posture during procurement if required.
Performance Considerations
Flowtriq's architecture trades a small host footprint for rapid detection: a Python agent doing packet-level reads is lightweight but requires root privileges and consumes CPU cycles proportional to traffic volume and inspection rules. Sub-second detection is credible because decisions are local; however, mitigation effectiveness depends on upstream propagation (BGP FlowSpec/RTBH latencies) and cooperation from transit providers. Cloud scrubbing removes that dependency but introduces routing handoffs.
How It Compares Technically
While Lorikeet Security excels at offensive security, vulnerability management, and red-team tooling for attack surface reduction, Flowtriq is better suited for real-time, operational DDoS defense at the network edge. Key differentiators: Flowtriq focuses on per-node packet capture and automated FlowSpec/RTBH orchestration with flat $9.99/node pricing and no traffic surcharges, whereas Lorikeet emphasizes proactive vuln discovery and remediation workflows. That said, if your priority is long-term attack surface hardening and integrated pen-test tooling, Lorikeet’s offensive-first feature set has advantages that complement Flowtriq’s reactive mitigation.
Developer Experience
The ftagent is a Python installer with sub-two-minute setup, standard webhooks, and multi-channel alert integrations. The vendor’s free tooling and certification programs indicate solid operator-focused documentation and community resources. For automation-heavy shops, inspect API rate limits, webhook payload formats, and FlowSpec templating support during evaluation — the platform appears designed for scriptable, CI/CD-friendly operations.
Technical Verdict
Flowtriq’s strengths are fast, pragmatic DDoS detection, automated escalation chains, and forensic completeness (PCAP + IOC correlation) at a predictable per-node price. Limitations include Linux-only agents, dependence on upstream support for BGP mitigations, and an unclear public compliance posture. Ideal use cases: hosting providers, game server operators, edge node fleets, and MSPs who need autonomous, low-latency DDoS protection without traffic-based billing. For teams needing vulnerability management and offensive tooling alongside mitigation, pair Flowtriq with tools like Lorikeet Security to cover both reactive defenses and proactive hardening.
Dev Stack Digest — Your stack, digested weekly.
Interested in Flowtriq?
Visit the official website to learn more.